访问查看
得到下方源码
<?php
$miwen="a1zLbgQsCESEIqRLwuQAyMwLyq2L5VwBxqGA3RQAyumZ0tmMvSGM2ZwB4tws";
function encode($str){
$_o=strrev($str);
// echo $_o;
for($_0=0;$_0<strlen($_o);$_0++){
$_c=substr($_o,$_0,1);
$__=ord($_c)+1;
$_c=chr($__);
$_=$_.$_c;
}
return str_rot13(strrev(base64_encode($_)));
}
highlight_file(__FILE__);
/*
逆向加密算法,解密$miwen就是flag
*/
?>
其中用到了一个没有见过的str_rot13()方法,了解后如下

奖该上述的代码反过来写一遍即可
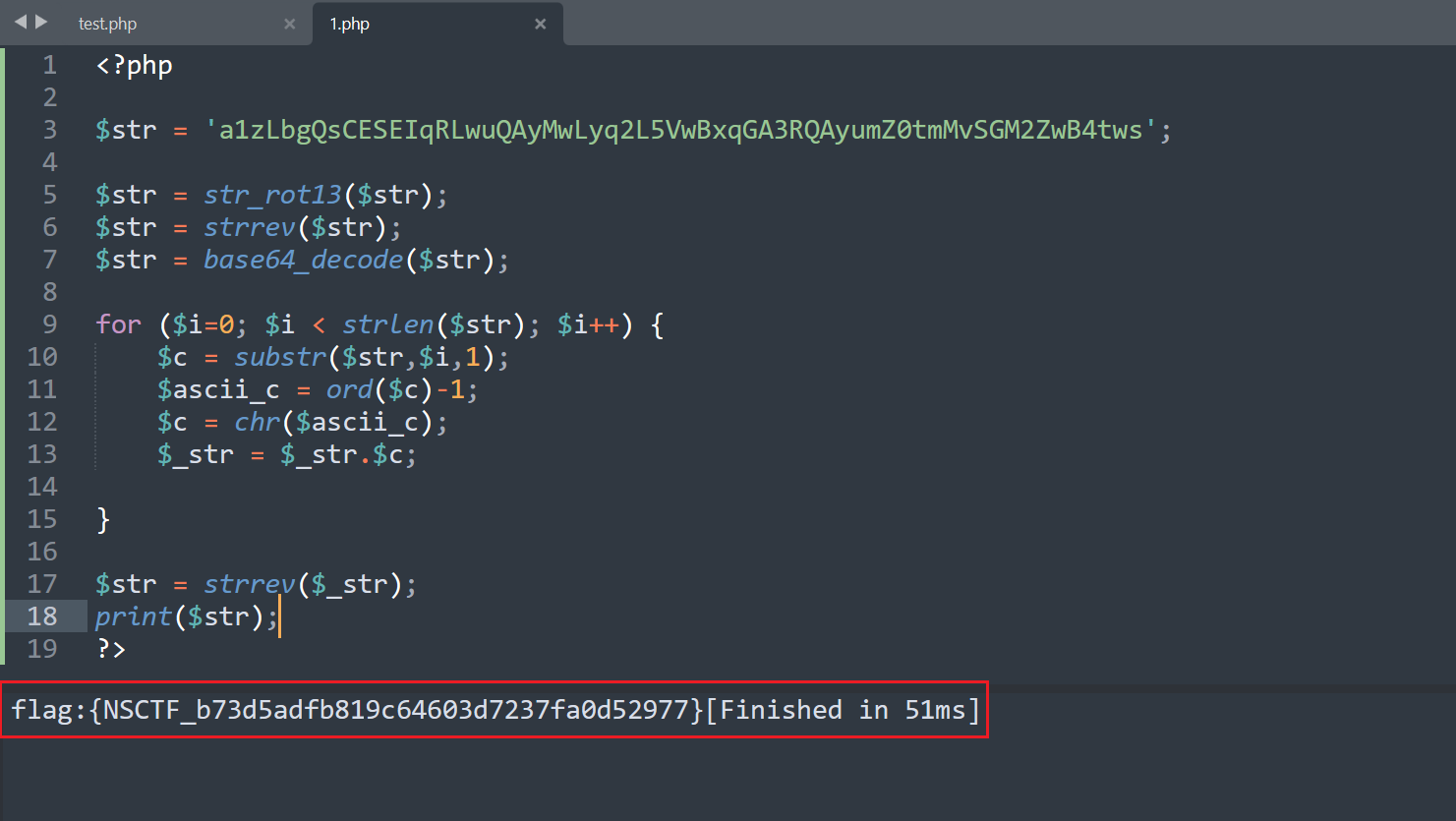
<?php
$str = 'a1zLbgQsCESEIqRLwuQAyMwLyq2L5VwBxqGA3RQAyumZ0tmMvSGM2ZwB4tws';
$str = str_rot13($str);
$str = strrev($str);
$str = base64_decode($str);
for ($i=0; $i < strlen($str); $i++) {
$c = substr($str,$i,1);
$ascii_c = ord($c)-1;
$c = chr($ascii_c);
$_str = $_str.$c;
}
$str = strrev($_str);
print($str);
?>