Memory Safety
Buffer overflow vulnerabilities
You should keep only 61C's config (not 161's config), and when SSHing, you need to explicitly type the usernames: ssh cs61c-xyz@hive22 or ssh cs161-xyz@hive22.
ebp always points to sfp.
看以下这个例子
char buf[8];
int authenticated = 0;
void vulnerable() {
gets(buf);
}
由于 gets(buf) 不会检查,所以可能导致缓冲区溢出
比如如果攻击者可以将 9 个字节的数据写入 buf (第 9 个字节设置为非零值),则会将 authenticated 标志设置为 true,并且攻击者将能够获得访问权限。
被覆盖的也可以是一个指向地址的指针,这样就会在试图跳转到原本指向的地址时跳转到覆写的任何地址上,从而执行一些恶意指令
void func(int len, char *data){
}
memcpy 中的 size_n 是 unsigned 的
Cryptography
In a nutshell, cryptography is about communicating securely over insecure communication channels.
Introduction
这里有个攻击 CS61A 考试的 Lab,如果想做的话可以发邮件给 Maddie
Definition
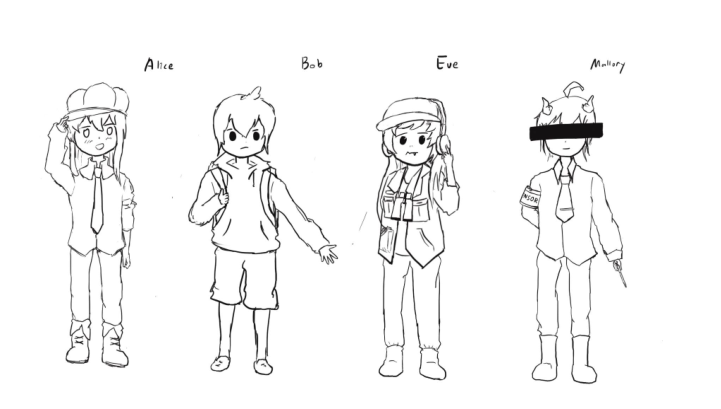
几个主要角色:
- Alice and Bob: The main characters trying to send messages to each other
over an insecure communication channel (之后还会有 Carol 和 Dave) - Eve: An eavesdropper who can read any data sent over the channel (也被称为 honest-but-curious attacker)
- Mallory: A manipulator who can read and modify any data sent over the
channel (也被称为 malicious attacker)
三大属性:
-
Confidentiality(机密性): An adversary cannot read our messages.
-
Integrity(完整性): An adversary cannot change our messages without being detected.
-
Authenticity(真实性): I can prove that this message came from the person who
- 注意真实性依赖于完整性(如果信息被篡改,无论信息来源如何都没有意义)